Staff Reporter
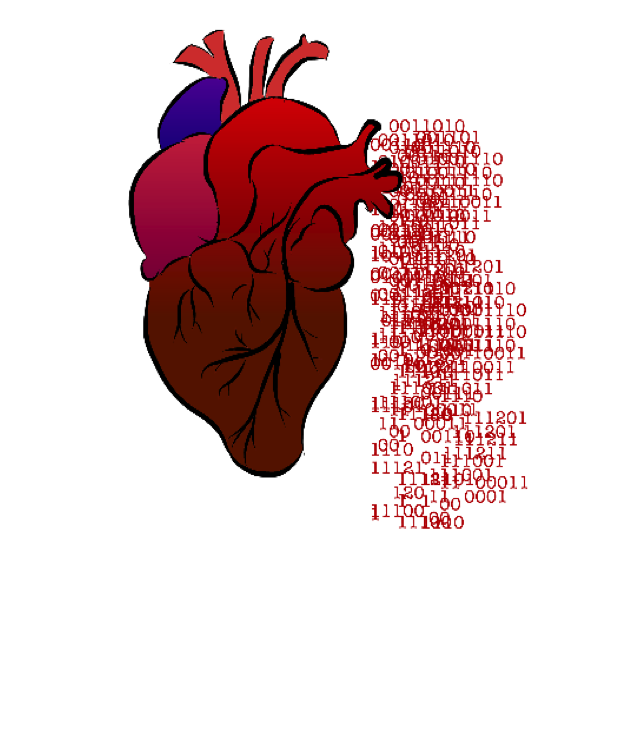
A security flaw in a wide range of web servers known as Heartbleed has led many individuals to fear for the security of their personal information on the internet.
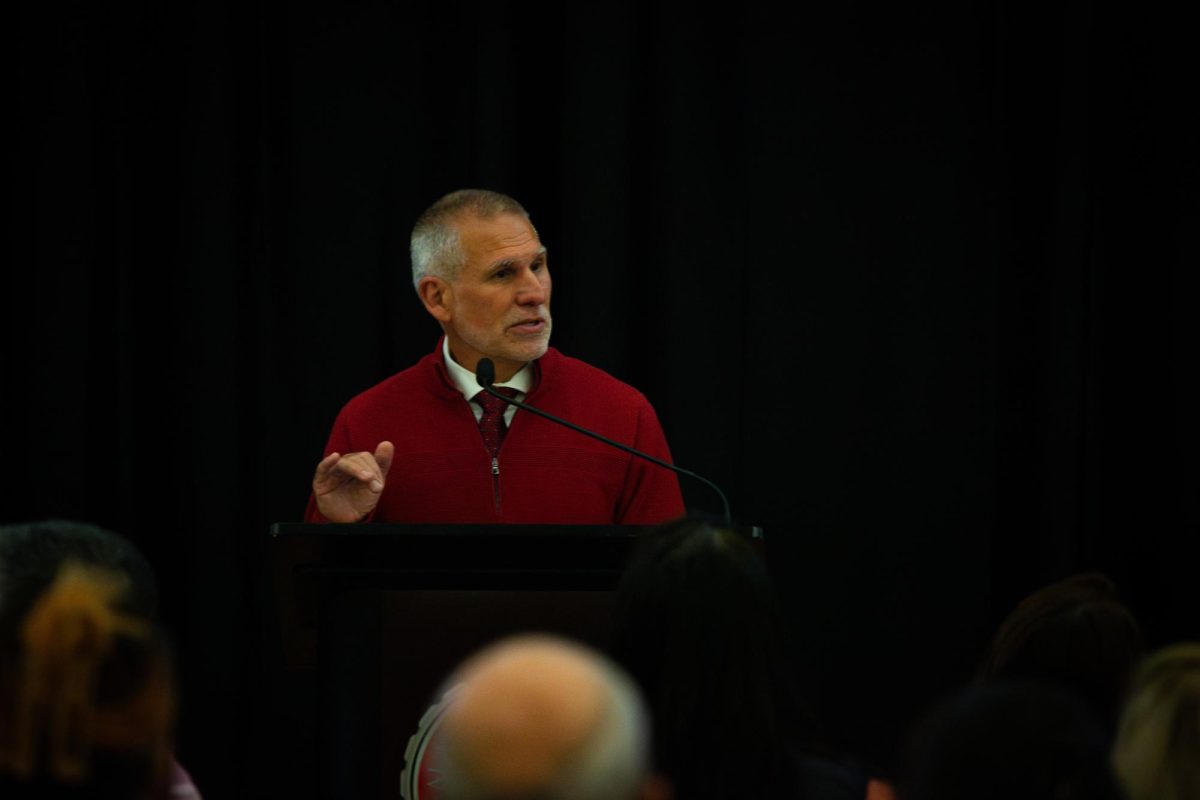
According to Andreas Bohman, assistant vice president of Information Security at Central, Heartbleed is a vulnerability, or bug, in OpenSSL, a system commonly used to secure communication. Heartbleed was introduced as a mistake in 2012 and was not detected until a security researcher with Google found the vulnerability two years later.
“[Heartbleed] became a big deal because it is an extensive vulnerability,” Bohman said. “It allows someone to essentially read confidential information off the server, including passwords and usernames.”
One of the reasons this particular bug has become such a threat is because of its impact. Internet users who take advantage of Facebook, Gmail, Amazon and other similarly popular websites, are using the same kind of software. Any accounts using the software could be affected, according to Chris Timmons, a senior network engineer in Information Services at Central.
“The potential number of individuals that would be affected by this would be in the millions,” Timmons said.
Part of the problem with the Heartbleed vulnerability, according to David Hart, network engineer and interim director of networks and operations, is that the vulnerability looks like normal traffic.
Central uses the OpenSSL program and was potentially vulnerable to Heartbleed, but the school’s reaction to the vulnerability was quick. Bohman says that as soon as Information Services found out about the vulnerability, they started a scan internally and externally for a range of OpenSSL versions from 1.0.1 through 1.0.1f.
“The good news is that all our outfacing critical web portals were not impacted,” Bohman said.
The scans found that some internal systems were impacted, but these systems were patched right away to prevent further compromise.
“Now we’re in the process of revoking and reissuing security certificates, because if someone had exploited this vulnerability internally,” Bohman said. “You can patch the system, but if they have your security certificate, even if it was patched, they’re still going to get in through the system.”
Student information was unaffected by Heartbleed. Central uses PeopleSoft to store student information to ensure their privacy. Some of the programs that were affected were administrative systems used to control the network, says Bohman. Those systems are only accessed by the Information Services personnel.
“None of our PeopleSoft environments were vulnerable to this particular vulnerability, and our student data was safe,” Bohman said.
To some of the Information Services team members, there is more good news to be found in the aftermath of Heartbleed and some benefits to reap from a vulnerability of this scale.
“[Heartbleed] means that some information that we thought was private, might not be private on the internet,” Hart said. “It also means the internet community is quick to react.”
There are websites with lists of which sites have and have not been affected, as well as what has been patched and what has not been patched, according to Hart.
Timmons believes this vulnerability brings a unique opportunity for internet user awareness outside of seeing only the benefits in the internet’s capabilities.
“The awareness that’s created by some of these events is beneficial,” Timmons said.